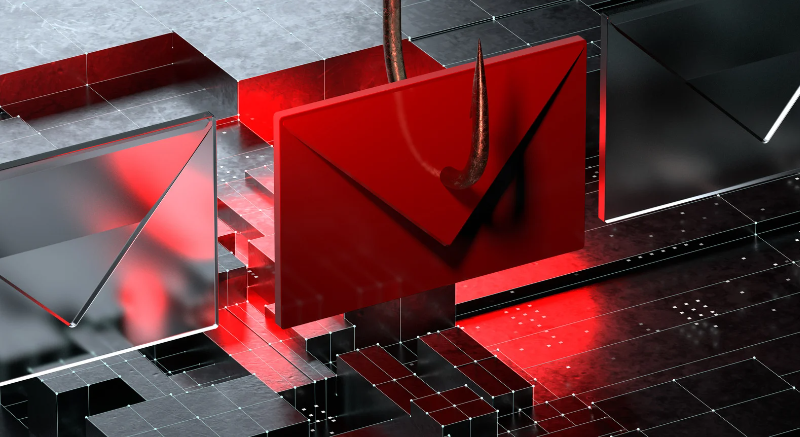
Introduction: In today’s digital landscape, phishing attacks have become increasingly prevalent and sophisticated, posing significant risks to individuals and organizations alike. Understanding the various types of phishing attacks and implementing effective defensive measures is crucial to safeguarding sensitive information. One powerful tool in the fight against phishing is a Data Loss Prevention (DLP) solution. In this blog post, we will delve into different phishing attack types, explore defensive measures, and highlight the importance of utilizing a robust DLP solution.
Exploring Phishing Attack Types:
Phishing attacks come in various forms, each with its own methodology and objectives. By familiarizing ourselves with these attack types, we can better prepare ourselves to defend against them.
- Deceptive Phishing: Deceptive phishing involves creating fraudulent emails that mimic reputable organizations to trick recipients into revealing sensitive information such as passwords or credit card details. Attackers often employ social engineering techniques to exploit human vulnerabilities and increase the likelihood of success.
- Spear Phishing: Spear phishing attacks are highly targeted and personalized, designed to deceive specific individuals or organizations. Attackers conduct extensive research to tailor their messages and increase the chances of success. These attacks often appear to come from trusted sources, making them harder to detect.
- Clone Phishing: Clone phishing involves creating malicious copies of legitimate emails or websites. Attackers duplicate and modify genuine communications, adding malicious elements or redirecting users to fake websites. The goal is to deceive recipients into disclosing sensitive information or downloading malware-infected attachments.
Implementing Defensive Measures
To effectively protect against phishing attacks, organizations and individuals must adopt proactive defensive measures. By combining multiple strategies, a strong defense can be established:
- User Education and Awareness: Promoting security awareness and providing regular training sessions can empower individuals to identify phishing attempts, recognize suspicious emails, and understand best practices for handling sensitive information.
- Robust Email Filtering: Implementing advanced email filtering solutions can help identify and block phishing emails before they reach users’ inboxes. Leveraging machine learning algorithms and threat intelligence, these filters can detect suspicious patterns and known phishing indicators.
- Multi-Factor Authentication (MFA): Enforcing MFA adds an extra layer of security, requiring users to provide additional verification beyond passwords. This can include one-time passwords, biometric authentication, or physical security tokens, making it more challenging for attackers to gain unauthorized access.
- Regular Software Updates: Keeping all software, including operating systems and applications, up to date is crucial. Software updates often include security patches that address known vulnerabilities, reducing the risk of successful phishing attacks.
- Incident Response Planning: Developing an incident response plan ensures organizations can effectively respond to and mitigate phishing attacks. This includes defining roles and responsibilities, establishing communication channels, and regularly testing the plan through simulated exercises.
The Power of DLP Solutions
While each defensive measure plays a vital role, deploying a robust Data Loss Prevention (DLP) solution significantly enhances an organization’s security posture. DLP solutions provide comprehensive protection against data breaches resulting from phishing incidents. Here’s how they work:
- Monitoring and Control: DLP solutions monitor and control the movement of sensitive data within the organization’s network. By defining policies and rules, these solutions can detect and prevent unauthorized access, ensuring that sensitive information remains secure.
- Data Encryption: DLP solutions often include encryption capabilities, ensuring that sensitive data is protected both at rest and in transit. Encryption adds an additional layer of security, making it significantly harder for attackers to access or exploit the stolen information.
- Data Loss Prevention Policies: DLP solutions enable organizations to create and enforce policies that govern how sensitive data is handled. These policies can automatically detect and block suspicious activities, such as unauthorized data transfers or email communications containing sensitive information.
- Endpoint Protection: Many DLP solutions offer endpoint protection, monitoring and securing data on individual devices. This helps prevent data leakage or unauthorized transfer through removable storage devices, cloud storage applications, or email clients.
- Threat Intelligence Integration: Integrating DLP solutions with threat intelligence feeds enhances their effectiveness in detecting and mitigating phishing attacks. By leveraging real-time threat intelligence, DLP solutions can identify and block phishing emails, malicious attachments, or suspicious URLs, providing an additional layer of defence
- Data Classification and Tagging: DLP solutions often provide capabilities for data classification and tagging. By categorizing data based on its sensitivity level, organizations can apply different levels of protection and control. This ensures that sensitive information receives the highest level of security measures.
Protecting against phishing attacks is paramount in today’s digital landscape. By understanding the various types of phishing attacks and implementing a combination of defensive measures, organizations and individuals can significantly reduce their vulnerability to such threats. Additionally, leveraging the power of a robust Data Loss Prevention (DLP) solution adds an extra layer of security and helps ensure the protection of sensitive data.
By continuously educating and raising awareness among users, implementing strong email filtering, utilizing multi-factor authentication, keeping software up to date, and having a well-defined incident response plan, organizations can fortify their defences against phishing attacks. Furthermore, integrating a DLP solution provides advanced monitoring, data encryption, and policy enforcement to mitigate the risks associated with phishing incidents.
Protecting sensitive information requires a proactive and multi-layered approach. By staying vigilant, implementing best practices, and leveraging advanced technologies like DLP solutions, organizations can mitigate the impact of phishing attacks and safeguard their valuable data assets.
Remember, prevention and preparedness are key in the ongoing battle against phishing attacks. Stay informed, stay proactive, and stay protected.
Note: This blog post provides an overview of phishing attack types, defensive measures, and the benefits of DLP solutions. For more in-depth information and specific implementation guidance, please consult with cybersecurity experts and refer to official documentation from reputable sources.
References: https://perception-point.io/guides/phishing/phishing-types-attacks-6-defensive-measures/#Use_a_DLP_Solution